Your emails may be sending fine — but without proper authentication, inbox providers have no reason to trust them. Gmail, Outlook, and every major mail provider run a background check on every message before it reaches the inbox. If your domain cannot prove it sent the email, that message goes to spam, gets quarantined, or is silently rejected. No error. No notification. Just missing email.
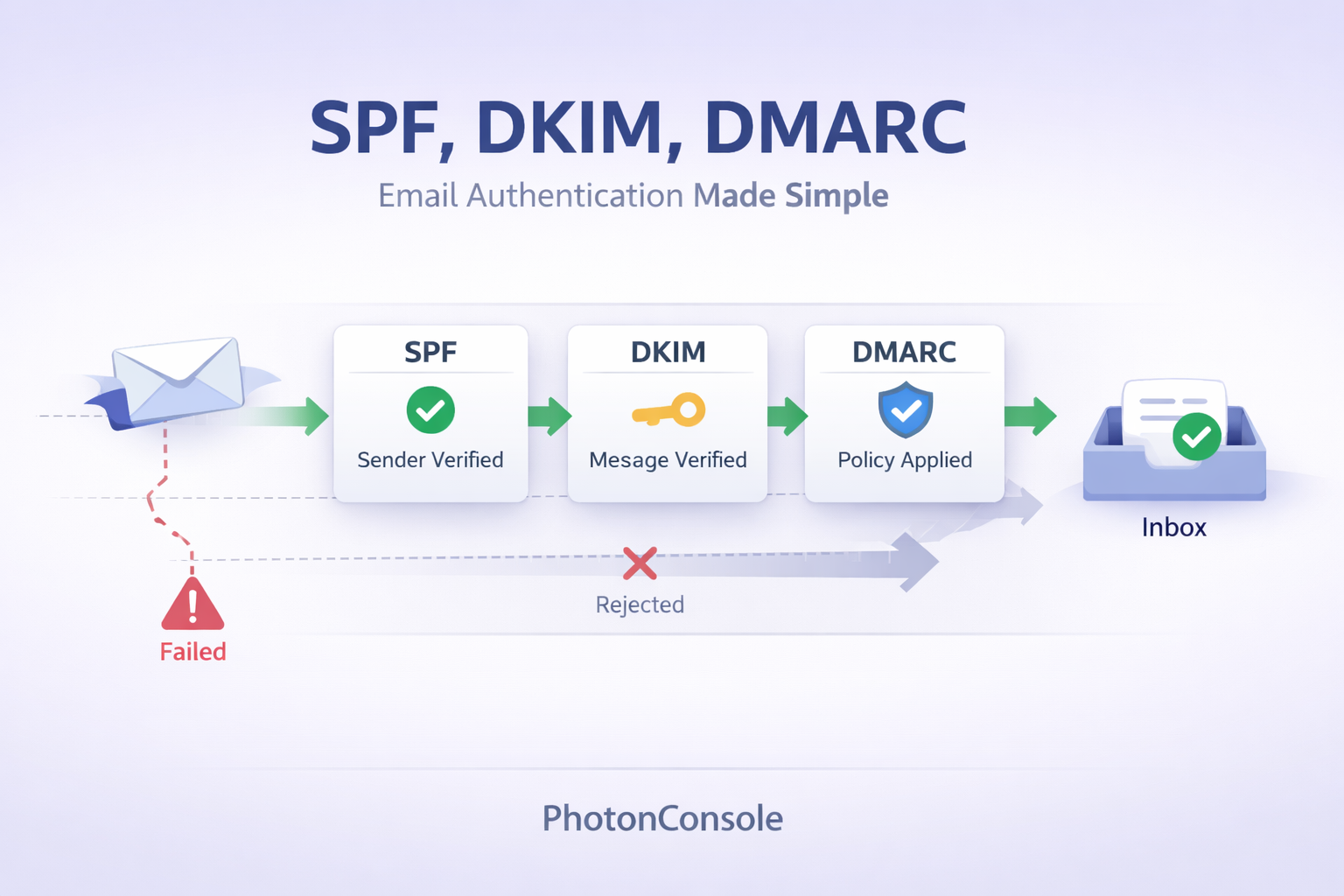
SPF-DKIM-DMARC are the three DNS-based records that pass that background check. Understanding what each one does — and how they work together — is the foundation of reliable email delivery. If your email deliverability is inconsistent, this is the first place to look.
Quick Answer: What Are SPF, DKIM, and DMARC?
- SPF (Sender Policy Framework): A DNS record that specifies which mail servers are authorized to send email on behalf of your domain. It answers the question: who is allowed to send from this domain?
- DKIM (DomainKeys Identified Mail): A cryptographic signature attached to every outgoing message. It verifies that the email was not altered in transit and genuinely came from your domain.
- DMARC (Domain-based Message Authentication, Reporting, and Conformance): A policy record that ties SPF and DKIM together, defines what happens when either check fails, and enables reporting so you can monitor authentication results across your domain.
All three work at the DNS level. None of them require changes to your email content. They are configuration records — and getting them right is one of the highest-impact, lowest-effort improvements you can make to your sending infrastructure.
Why Email Authentication Matters
Inbox providers cannot read your mind. When an email arrives claiming to be from support@yourcompany.com, the receiving server has no inherent way to know whether it actually came from you or from a bad actor spoofing your domain. Authentication records give them a verifiable way to check.
Beyond preventing spoofing and phishing, authentication directly affects inbox placement. Most SMTP errors and authentication failures are configuration problems — and they are entirely preventable. Providers like Gmail now enforce authentication requirements for bulk senders, and the threshold for what counts as bulk is lower than most teams expect. Even transactional email at moderate volumes can be affected.
Authentication is not optional infrastructure. It is the baseline requirement for trusted email communication.
What Is SPF?
Think of SPF as a guest list at the door of a venue. Your domain publishes a list of approved mail servers — and when an email arrives claiming to be from your domain, the receiving server checks whether the sending IP is on that list. If it is, the email passes SPF. If it is not, the check fails.
SPF is a DNS TXT record that looks something like this:
v=spf1 include:photonconsole.com ~allThe include directive tells receiving servers to check PhotonConsole’s authorized IPs in addition to your own. The ~all at the end means that mail from unlisted servers should be treated as a soft fail — accepted but marked as suspicious. Changing it to -all is a hard fail: reject everything not on the list.
SPF alone has a limitation worth knowing: it only checks the server the email came from, not the From address the recipient sees. That gap is part of why DKIM and DMARC exist.
What Is DKIM?
DKIM works like a wax seal on a letter. Before your mail server sends a message, it applies a cryptographic signature using a private key. Your DNS record publishes the matching public key. When the receiving server gets the message, it uses that public key to verify the signature — confirming both that the email came from your domain and that nobody tampered with it in transit.
If the signature does not match — because the message was modified, because it came from an unauthorized server, or because the keys are misconfigured — DKIM fails. The receiving server treats the message as suspect.
DKIM is configured through your SMTP provider. They generate the key pair, give you the public key as a DNS TXT record to publish, and handle the signing on every outgoing message. If you are handling your own mail server, this requires manual configuration — one of the reasons teams move to a managed SMTP relay service that handles signing automatically.
What Is DMARC?
DMARC is the rulebook that governs SPF and DKIM. It does three things: it tells receiving servers what to do when SPF or DKIM fails, it requires that authentication results align with your actual From address, and it enables reporting so you can see what is happening across your domain.
A basic DMARC record looks like this:
v=DMARC1; p=quarantine; rua=mailto:dmarc-reports@yourdomain.comThe p= value is the policy. Options are:
p=none— Monitor only. No action taken on failures. Good starting point.p=quarantine— Failed messages go to spam.p=reject— Failed messages are blocked entirely.
The rua address receives aggregate reports showing authentication results for all email claiming to be from your domain — including any spoofing attempts.
How SPF-DKIM-DMARC Work Together
Here is what happens when an email is received:
- The receiving server checks whether the sending IP is listed in your SPF record.
- It verifies the DKIM signature against the public key in your DNS.
- It checks DMARC alignment — whether the domain in the SPF or DKIM check matches the From address visible to the recipient.
- Based on your DMARC policy, it decides whether to deliver, quarantine, or reject the message.
All three checks must pass — and they must be aligned. SPF passing for a subdomain while your From address uses the root domain will fail DMARC alignment even though the individual check succeeded. This is one of the most common and confusing authentication failures teams encounter.
For a full walkthrough of what authentication failures look like in practice and how to resolve each type, the SMTP 535 authentication error guide covers the most common scenarios with specific fixes.
Common Mistakes That Break Authentication
Most authentication problems are not caused by misunderstanding the standards — they are caused by small configuration errors that are easy to miss:
- Incorrect SPF record with too many DNS lookups: SPF has a hard limit of 10 DNS lookups. Using multiple
includedirectives for different sending services can exceed this limit, causing the SPF check to fail with apermerror. - Missing DKIM record after switching providers: When you move to a new SMTP provider, you need to publish a new DKIM public key in your DNS. Old keys do not transfer. Emails signed with keys that no longer exist in DNS will fail DKIM.
- Leaving DMARC at
p=noneindefinitely: Setting DMARC to monitor-only is a useful starting point, but it provides no protection. Domains sitting onp=nonefor months are fully exposed to spoofing. Move top=quarantineonce you have reviewed your reporting data and confirmed legitimate email is passing. - DMARC alignment failures: SPF and DKIM both pass, but the domains they authenticate do not align with the From address. This silently fails DMARC even though the individual checks show green. Verify alignment explicitly — not just individual pass/fail results.
How to Set Up SPF, DKIM, and DMARC
Step 1: Add Your SPF Record
In your domain’s DNS settings, add a TXT record at the root domain (@) with your SPF value. Include all services that send email on your behalf — your SMTP provider, your CRM, any third-party tools. Keep the total under 10 DNS lookups. Use ~all initially while you verify coverage, then tighten to -all once confirmed.
Step 2: Configure DKIM Through Your SMTP Provider
Your SMTP provider will supply a DKIM public key as a DNS TXT record, typically at a subdomain like mail._domainkey.yourdomain.com. Add it exactly as provided. Allow up to 48 hours for DNS propagation before testing.
Step 3: Publish Your DMARC Record
Add a TXT record at _dmarc.yourdomain.com. Start with p=none and a reporting address. After reviewing reports for two to four weeks and confirming that legitimate mail is passing, move to p=quarantine. Review again before moving to p=reject.
Step 4: Test and Verify
Use MXToolbox to check each record independently. Send a test message to Mail-Tester to get a full authentication and spam score report. Verify that SPF, DKIM, and DMARC all show as passing — and check alignment specifically, not just individual results.
For a complete testing process beyond authentication, the SMTP server testing guide walks through the full diagnostic flow from connection to delivery.
Quick Fix: Authentication Failing Despite Correct Records
- Check DMARC alignment — not just SPF and DKIM pass/fail individually
- Verify the From domain matches the domain used in SPF and DKIM signing
- Confirm DNS changes have fully propagated (use MXToolbox, not your registrar’s preview)
- Count your SPF DNS lookups — exceeding 10 causes a silent permerror
Real Problems We See in Production
Authentication configuration looks simple on paper. In practice, these are the failure patterns that come up most consistently:
- SMTP delivers successfully but DMARC fails: The message was accepted and delivered — then routed to spam because DMARC alignment failed. The application log shows no error. The only way to catch it is DMARC reporting or a recipient complaint.
- SPF passes but emails still land in spam: SPF passing does not guarantee inbox placement. If DKIM is missing or DMARC is failing alignment, spam filters still apply negative scoring. Authentication is a necessary condition, not a sufficient one.
- DKIM breaks after a DNS migration: Migrating DNS to a new registrar or provider without transferring all TXT records is one of the most common causes of sudden authentication failure. DKIM records are easy to overlook because they sit on subdomains, not the root.
These issues — and the broader patterns behind them — are covered in the full Gmail spam analysis, which connects authentication failures to real inbox placement outcomes.
When Authentication Alone Is Not Enough
Authentication proves your identity. It does not build your reputation. A domain with perfect SPF, DKIM, and DMARC configuration but a history of high bounce rates, spam complaints, or sudden volume spikes will still face inbox placement problems. Authentication is the entry requirement — sender reputation determines how well you perform once you are past it.
This is why deliverability is an infrastructure problem, not just a configuration checklist. The sending IP you use, the quality of your list, the consistency of your sending volume, and the engagement signals your messages generate all feed into how inbox providers score you over time. Understanding this full picture is what separates teams with reliable delivery from teams that are constantly chasing down missing emails. The SMTP troubleshooting guide covers the infrastructure-level failures that authentication alone cannot prevent.
Where PhotonConsole Handles This For You
Setting up authentication records correctly is a one-time task. Keeping them correct as your infrastructure changes — new sending services, domain migrations, key rotations — requires ongoing attention that most development teams do not have bandwidth for.
PhotonConsole is a dedicated transactional email service that manages DKIM signing automatically on every outgoing message, provides configuration guidance for SPF and DMARC alignment, and surfaces authentication failures in real-time delivery logs before they become reputation problems. For teams that need email to work reliably without managing the authentication layer manually, it removes that operational burden entirely. The pricing model scales with your actual sending volume — no flat monthly commitment required.
Frequently Asked Questions
What happens if SPF fails?
When SPF fails, the receiving server knows the email came from a server not authorized by your domain’s DNS. Depending on your DMARC policy, the message may be delivered to spam, quarantined, or rejected outright. With no DMARC record, behavior varies by provider — most will apply additional spam scoring rather than hard-rejecting.
Can DKIM work without SPF?
Technically yes — DKIM can pass independently of SPF. However, DMARC alignment requires at least one of them to pass and align with the From address. Relying on DKIM alone without SPF leaves a gap: if DKIM fails for any reason, there is no backup authentication layer. Best practice is to have both configured correctly.
What is DMARC alignment?
DMARC alignment means the domain authenticated by SPF or DKIM must match the domain in the From address that recipients see. Passing SPF for mail.yourdomain.com while sending from yourdomain.com will fail strict DMARC alignment. Relaxed alignment (the default) allows subdomain matches. Strict alignment requires an exact match.
Do I need all three — SPF, DKIM, and DMARC?
Yes. SPF alone prevents basic IP spoofing but does not verify message integrity. DKIM alone signs the message but does not tell providers what to do if it fails. DMARC ties both together, enforces policy, and provides visibility through reporting. All three are required for a complete, trusted authentication setup that meets current sender guidelines from Google and Microsoft.
Conclusion
Without authentication, your emails are just messages. With it, they become trusted communication — verified by your domain, protected from tampering, and backed by a policy that tells inbox providers exactly how to treat them. SPF, DKIM, and DMARC are not advanced configuration for large enterprises. They are the baseline requirement for any domain that sends email and expects it to arrive.
Configure all three, verify alignment, monitor your DMARC reports, and build on that foundation with clean sending infrastructure. That combination is what consistent inbox placement is built on.







Best Mailgun Alternatives In 2025: A Decision-Driven Comparison For Developers And Growing Teams | Photonconsole.com
April 1, 2026[…] SPF, DKIM, DMARC Explained Simply […]
Email API: Powerful & Reliable Sending Solution
April 1, 2026[…] setups — become nearly impossible. If you are setting up authentication for the first time, the plain-language guide to SPF, DKIM, and DMARC is the fastest way to get it […]
What Is SMTP? Direct Answer + Easy Guide | Photonconsole
April 1, 2026[…] full setup walkthrough for all three records lives in SPF, DKIM, and DMARC explained simply. For a complete deliverability strategy covering IP reputation, list hygiene, content scoring, and […]
Free SMTP Servers (Limits, Failures & What Breaks In Production) | Photonconsole.com
April 1, 2026[…] Authenticate your domain before sending a single email SPF, DKIM, and DMARC must be live in DNS. Skipping this is the single fastest path to the spam folder. Full setup guide → […]
Emails Sent But Not Delivered? Fix It Fast | Photonconsole
April 1, 2026[…] These three records work together to prove that you are who you say you are. Missing even one of them significantly increases the chance of non-delivery. For a plain-language explanation of all three, see this guide on SPF, DKIM, and DMARC explained simply. […]
Why Are My Emails Delayed? Causes, Diagnosis, And Fixes | Photonconsole.com
April 1, 2026[…] a detailed explanation of how these protocols work together, see SPF, DKIM, and DMARC Explained Simply. The DMARC.org FAQ is also a reliable reference for understanding policy […]
SMTP Relay For Transactional Emails: How To Choose The Right One | Photonconsole.com
April 1, 2026[…] The full breakdown of how authentication records affect delivery is in our guide on SPF, DKIM, and DMARC explained. […]
SMTP Testing Methods: Why Your Tests Pass But Emails Fail
April 1, 2026[…] providers. DNS misconfiguration is one of the most common root causes of spam placement. The SPF, DKIM, and DMARC explained guide covers exactly how alignment failures produce spam placement even when individual authentication […]
SMTP Configuration Step By Step: The Complete Setup Guide | Photonconsole.com
April 1, 2026[…] SPF, DKIM, and DMARC authentication records are closely tied to your sender address. If the domain in your From address does not match your authentication records, your emails will face deliverability problems regardless of how correctly the SMTP connection itself is configured. The full setup process for these records is covered in our guide on SPF, DKIM, and DMARC explained. […]
SMTP Configuration Guide (2026): Settings, Ports & Setup
April 1, 2026[…] SPF, DKIM, and DMARC authentication records are closely tied to your sender address. If the domain in your From address does not match your authentication records, your emails will face deliverability problems regardless of how correctly the SMTP connection itself is configured. The full setup process for these records is covered in our guide on SPF, DKIM, and DMARC explained. […]
How To Reduce Email Bounce Rate For SaaS Applications: A Technical Guide | Photonconsole.com
April 1, 2026[…] Fix: Publish a valid SPF record authorizing your relay’s sending IP ranges. Configure DKIM signing per sending domain using a 2048-bit key. Set DMARC to p=none with a reporting address, review aggregate reports, then advance to p=quarantine. The full configuration process is in the SPF, DKIM, and DMARC configuration guide. […]
SMTP Monitoring Tools For Transactional Email Infrastructure: An Engineering Guide | Photonconsole.com
April 1, 2026[…] SPF, DKIM, and DMARC configuration guide covers correct implementation. Continuous record validation — not one-time setup — is what […]
How To Reduce Email Bounce Rate For SaaS Applications: A Production Infrastructure Guide | Photonconsole.com
April 1, 2026[…] it produces systematic authentication failures across all sending, not just isolated incidents. The SPF, DKIM, and DMARC configuration guide covers correct implementation and the continuous validation practices that prevent […]