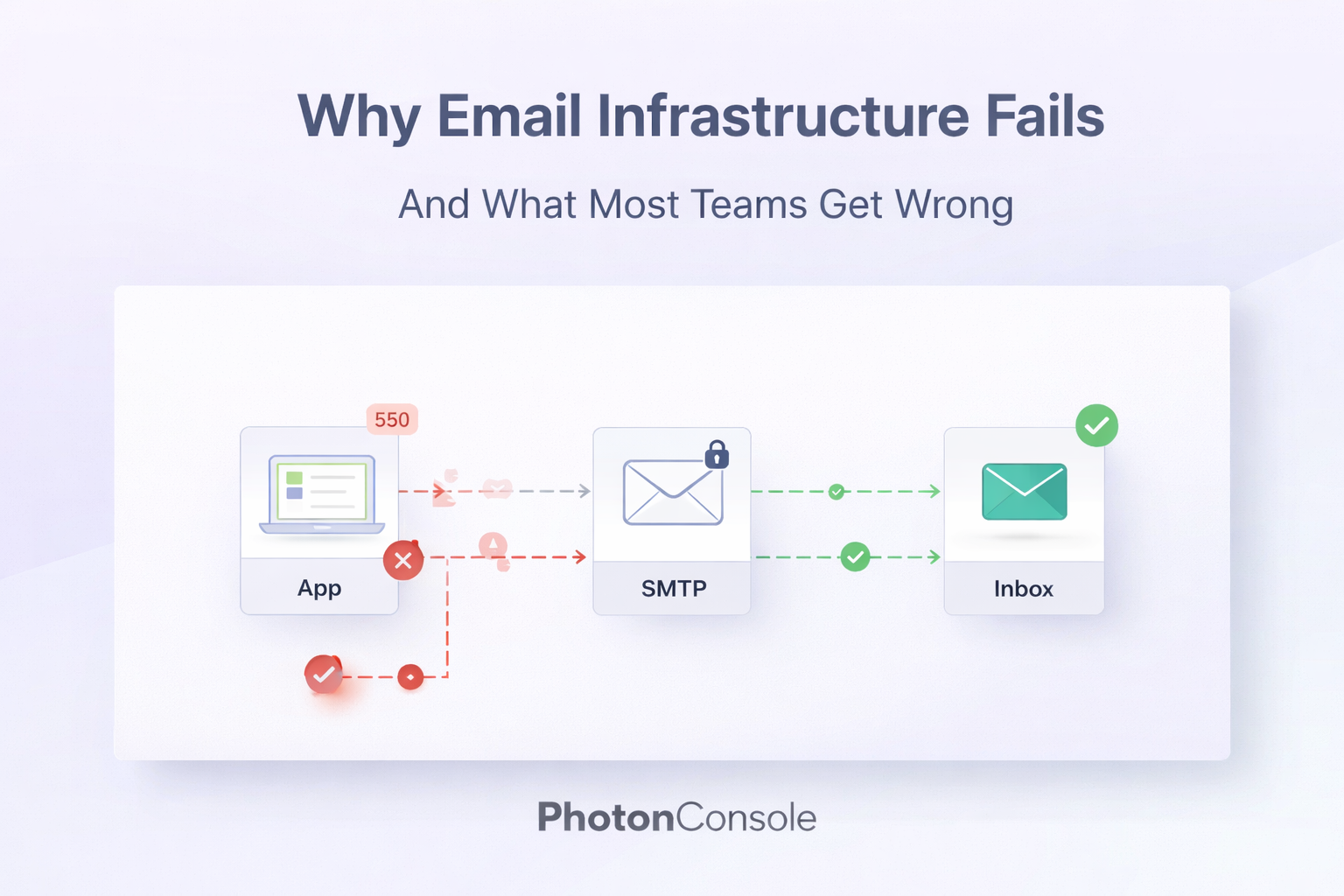
Most email failures do not crash your system. There is no error page. No alert. No notification. Your application keeps running, your users keep trying to log in, and somewhere between your server and their inbox, the OTP silently disappears.
This is what makes broken email infrastructure so dangerous. It does not fail loudly. It fails quietly, and users simply leave.
If you have ever received a support ticket that says “I never got the verification email” or “my password reset link never arrived,” you have already experienced the consequence of poor email infrastructure. The code worked. The delivery did not.
This post breaks down why email infrastructure fails, what most engineering and product teams consistently get wrong, and how to build a setup that actually works at scale.
Quick Answer: Why Do Emails Fail to Deliver?
Email delivery fails for several interconnected reasons. The most common causes are:
- Misconfigured SMTP settings or missing authentication records
- Sending from shared or blacklisted IP addresses
- Lack of SPF, DKIM, and DMARC records on the sending domain
- No monitoring or logging to detect failures early
- Using a development SMTP setup in a production environment
Most SMTP errors occur due to misconfiguration or authentication issues, not bugs in application code. The fix is almost always infrastructure-level, not application-level.
Why Email Infrastructure Fails
Email delivery looks simple from the outside. You call a function, pass an address, and the email goes out. Under the hood, however, email relies on a chain of protocols, DNS records, IP reputation systems, and third-party filtering engines. Any weak link in that chain causes failure.
1. Bad SMTP Configuration
Many teams configure SMTP once and never revisit it. A port mismatch, an expired credential, a wrong hostname, or a firewall rule that blocks outgoing connections on port 465 or 587 can silently drop every outgoing email without a clear error surfacing to the application layer.
Here is where most people mess up: they test email in development, it works, and they assume production will behave the same way. It often does not. Hosting providers, cloud platforms, and corporate networks handle outbound SMTP differently.
2. Missing Email Authentication
Authentication failures are one of the most common causes of email delivery issues. If your domain does not have SPF, DKIM, and DMARC records properly configured, receiving mail servers treat your messages with suspicion.
- SPF tells receiving servers which IPs are allowed to send email on behalf of your domain
- DKIM adds a cryptographic signature that proves the email was not tampered with in transit
- DMARC defines what happens when SPF or DKIM checks fail
Without these records, your emails may reach the inbox today and land in spam tomorrow, depending entirely on the receiving server’s current filtering policies. You can verify your domain’s authentication setup using tools like MXToolbox Email Health.
3. Shared IP Reputation Problems
When you send email through a basic hosting provider or a shared SMTP service, your messages go out from an IP address shared with hundreds or thousands of other senders. If any one of those senders behaves badly, their spam complaints affect your deliverability too.
This silently breaks your setup. You did nothing wrong, but your emails start landing in spam because someone else on the same IP was flagged.
4. No Understanding of Deliverability as a System
Deliverability is not a single setting you toggle. It is the cumulative result of domain reputation, IP reputation, content quality, sending volume consistency, and recipient engagement. Teams that treat it as a checkbox item almost always encounter problems when they start scaling.
Common Real-World Problems Teams Face
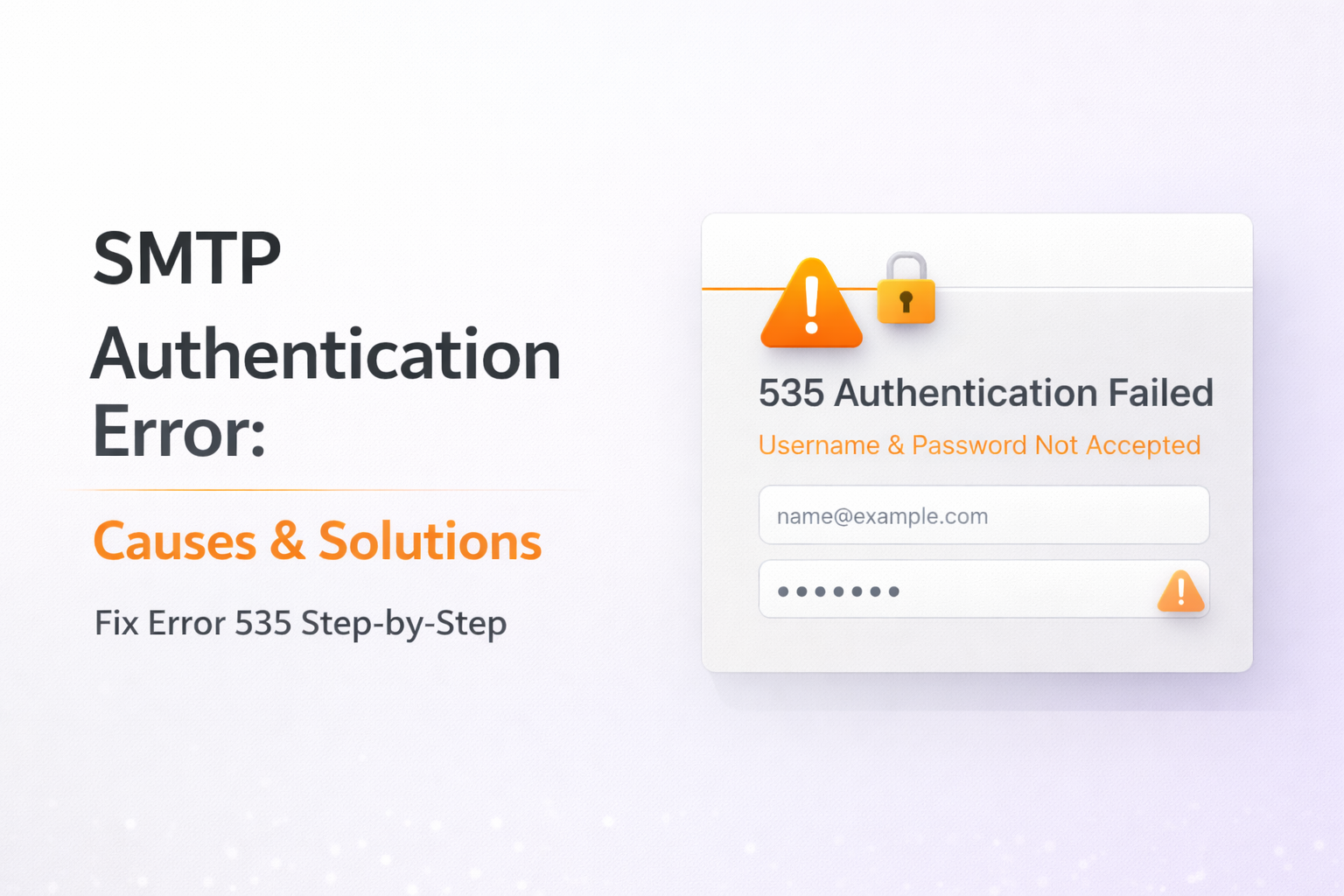
SMTP 535 Authentication Errors
A 535 error means the SMTP server rejected the login credentials. This happens when passwords change, when two-factor authentication is enforced on the sending account, or when app-specific passwords expire. These errors often appear suddenly after months of stable sending and take time to diagnose without proper logging.
Emails Going to Spam
This is the most reported and least understood email problem. Emails going to spam can be caused by any combination of poor sender reputation, missing authentication, low engagement rates, spammy content patterns, or being on a shared IP with a bad history. There is rarely a single cause, which makes diagnosis difficult without the right tools.
Google’s Gmail bulk sender guidelines provide a clear picture of what Gmail expects from senders, and Microsoft publishes similar guidance through their Microsoft 365 anti-spam documentation. Most teams have never read either.
Delayed Transactional Emails
OTP emails, password resets, and account verification messages have a short window to be useful. A 30-second delay in an OTP delivery is frustrating. A 5-minute delay causes users to abandon the flow entirely. Delays are typically caused by message queuing issues, rate limiting on the sending server, or throttling by the receiving domain.
What Most Teams Get Wrong
Treating Email as a Feature, Not Infrastructure
The most common mistake is categorizing email the same way you categorize a UI component or an API endpoint. A button can be broken and patched in the next deploy. Email infrastructure that fails can damage domain reputation in ways that take weeks or months to recover from.
Email is infrastructure. It needs to be planned, monitored, and maintained with the same seriousness as your database or your CDN.
Not Monitoring Delivery at All
Most teams have zero visibility into what happens after an email is sent. They know the function was called. They do not know if the message was delivered, bounced, deferred, or filtered as spam. Without delivery logs and bounce tracking, there is no way to detect a failure until a user reports it.
Ignoring the Infrastructure Layer Entirely
It is tempting to plug in a quick SMTP library and move on. But the infrastructure layer, meaning the IP reputation, the authentication setup, the sending domain configuration, and the relay architecture, is what determines whether your emails actually arrive. Skipping this work creates compounding problems as your sending volume grows.
Real Example: What One Team Experienced
Understanding these failures in theory is one thing. Seeing them play out in a real system is another.
Midgrow, a digital solutions company managing production systems for multiple clients, ran into exactly these issues. Their transactional email setup worked fine at low volumes. As usage scaled, OTP delays started appearing. Verification emails were landing in spam folders. SMTP errors began surfacing in logs with no clear pattern.
The root cause was not their application code. It was the infrastructure underneath it. They were sending through a basic SMTP setup with no dedicated relay, incomplete authentication records, and no real visibility into what was happening after emails were dispatched.
The way they diagnosed it, addressed it step by step, and rebuilt their email delivery layer is documented in detail in this real-world case study on fixing email infrastructure. It is worth reading if you are managing transactional email for any production system, because the problems they faced are not unique to them.
How to Fix Email Infrastructure the Right Way
Step 1: Use a Dedicated SMTP Relay
Stop sending email directly from your application server or through a shared hosting SMTP. A dedicated SMTP relay service gives you a dedicated sending infrastructure with managed IP reputation, proper authentication support, and delivery optimization built in.
Step 2: Set Up SPF, DKIM, and DMARC
These are not optional. Add an SPF record to your DNS that authorizes your sending service. Enable DKIM signing so that emails carry a verifiable signature. Set a DMARC policy so that receiving servers know how to handle failures. You can test your configuration at mail-tester.com before going live.
Step 3: Monitor Delivery Logs Actively
Every email you send should generate a log entry. You need to track at minimum: delivery status, bounce events, soft bounce reasons, and spam complaint rates. Without this data, you are flying blind.
Step 4: Scale Gradually and Warm Up New IPs
If you are moving to a new sending domain or IP, warm it up gradually. Start with a small volume, build a positive sending history, and increase volume over two to four weeks. Jumping straight to high-volume sending on a new IP is one of the fastest ways to get flagged by spam filters.
Step 5: Separate Transactional and Marketing Email Streams
Transactional emails (OTPs, alerts, confirmations) and marketing emails (newsletters, promotions) should go through separate sending streams. A high unsubscribe rate on a marketing campaign should never affect the deliverability of your OTP emails.
Quick Fix: Checklist for Email Infrastructure
- SPF record added to DNS and includes your relay provider
- DKIM signing enabled and verified
- DMARC policy set to at minimum p=none with a reporting address
- Sending through a dedicated relay, not a shared SMTP server
- Bounce tracking and delivery logs active
- Transactional and marketing streams separated
- IP warm-up plan in place for new sending infrastructure
Where PhotonConsole Fits Into This
Building reliable email infrastructure from scratch is complex. Most teams do not have the time or resources to manage IP reputation, configure dedicated sending infrastructure, and maintain delivery monitoring alongside everything else they are building.
PhotonConsole is built specifically to handle the infrastructure layer. It provides a dedicated SMTP relay with high deliverability infrastructure, full authentication support, delivery logging, and a pay-as-you-use pricing model that works for startups and growing teams without locking you into enterprise contracts.
It integrates with Node.js, PHP, WordPress, and any platform that supports standard SMTP, which means your application code does not change. The infrastructure underneath it becomes significantly more reliable. If you want to evaluate it for your use case, the pricing page breaks down the cost structure clearly.
The goal is not to add complexity. It is to remove the part of the system that was silently failing.
Pro Tips for Keeping Email Infrastructure Healthy
- Set up delivery alerts: If your send volume drops suddenly, something is wrong. Alert on it like you would alert on a service going down.
- Review bounce logs weekly: Hard bounces to invalid addresses hurt your sender score. Clean your lists regularly.
- Never use a free Gmail or personal email as a from address for transactional email: This breaks DKIM alignment and causes spam filtering issues.
- Test before you launch: Every new email flow should be tested end-to-end in a staging environment that mirrors your production DNS and authentication setup.
- Document your SMTP configuration: When the person who set it up leaves the team, undocumented SMTP credentials and settings become a serious operational risk.
Related Issues to Be Aware Of
- SMTP 550 errors (recipient address rejected)
- SMTP 421 errors (service temporarily unavailable, often rate limiting)
- Reverse DNS misconfiguration causing delivery failures
- SSL/TLS handshake failures on port 465 vs 587
- Email header spoofing flags triggering spam filters
Frequently Asked Questions
Why are my transactional emails going to spam?
The most common reasons are missing or misconfigured SPF, DKIM, or DMARC records, sending from a shared or blacklisted IP, or using a domain with no established sending reputation. Authentication setup should be the first thing you check.
What is SMTP 535 error?
SMTP error 535 means authentication failed. The sending server rejected the username or password used to connect. This usually happens when credentials expire, change, or when the account requires app-specific passwords.
How do I improve email deliverability?
Start with proper SPF, DKIM, and DMARC configuration. Then move to a dedicated SMTP relay with managed IP reputation. Monitor bounce and complaint rates consistently and keep your email lists clean.
Should transactional and marketing emails use the same sending domain?
No. Use a subdomain or a separate domain for marketing email. This protects your primary transactional sending domain from reputation damage caused by marketing campaign metrics.
How long does it take to recover from a bad sender reputation?
It depends on severity, but typically two to six weeks of clean sending behavior is needed before spam filters start treating your domain favorably again. Prevention is significantly easier than recovery.
Conclusion
Reliable email delivery is not optional. It is foundational.
Every OTP that never arrives is a user who cannot log in. Every verification email that lands in spam is a registration that never completes. Every delayed transactional message is a moment of friction that erodes trust in your product.
The teams that avoid these problems are not the ones with the best application code. They are the ones who understood early that email is infrastructure, built it accordingly, and monitored it continuously.
The fixes are not difficult. They require the right setup, the right tooling, and consistent attention. Start with authentication, move to a dedicated relay, and add monitoring. That sequence alone resolves the majority of email delivery failures.